8 Malicious NPM Packages Stole Chrome User Data on Windows

JFrog researchers found eight malicious NPM packages using 70 layers of obfuscation to steal data from Chrome browser users on Windows. The attack highlights a growing threat to developers.
Cybersecurity researchers from JFrog Security Research have discovered eight malicious NPM packages. These packages are designed to attack Windows users on the Google Chrome browser and steal personal data.
These packages are a clear example of what is known as a supply chain attack, a growing risk in the software industry. This kind of attack happens when malicious code is secretly injected into a legitimate part of the software development process, like an open-source library, which is then used by many different developers. This allows the hackers to reach a huge number of people without directly hacking each one individually.
According to JFrog’s blog post, attackers hid their malicious code in the packages using a series of advanced techniques, including what experts call “multi-layered obfuscation,” to hide their true purpose.
The malicious code was buried under a total of “70 layers of code obfuscation,” making it extremely difficult to detect. What’s more, the code automatically downloaded and installed a specific version of Python on a victim’s machine. It then used that to run a hidden script. All this, without any user input or approval.
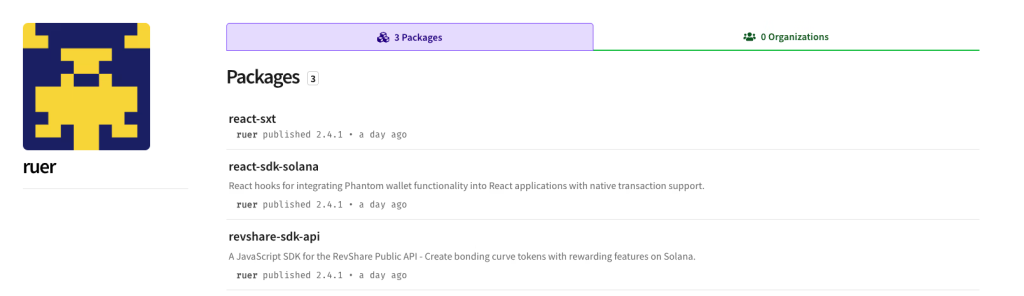
The final goal of this attack cycle was to steal sensitive data from the Chrome browser, including passwords, credit card information, cryptocurrency funds, and user cookies. The attackers behind this were an NPM user named “ruer” and another named “npjun.”
Open-source software repositories, as we know them, are becoming a prime target for attackers. Hackers are increasingly using tactics like typosquatting and masquerading, where they create packages with names similar to popular ones to trick developers into using them by mistake.
Nevertheless, JFrog researchers reported the incident, and all 8 malicious packages have been removed.
Guy Korolevski, a Security Researcher at JFrog and author of this report, shared his comment with Hackread.com, noting that the sophistication of these attacks shows why constant vigilance is necessary.
“The impact of sophisticated multi-layer campaigns designed to evade traditional security and steal sensitive data highlights the importance of having visibility across the entire software supply chain with rigorous automated scanning and a single source of truth for all software components,” he stated.
HackRead